
What is C:\NTLDR?
What is C:\BOOT.INI?
What is C:\NTDETECT.COM?
What is C:\WINDOWS\SYSTEM32\NTOSKRNL.EXE?
What is C:\BOOTMGR.EXE?
What is C:\BCD.DAT?
What is C:\WINDOWS\SYSTEM32\WINLOAD.EXE?
What is C:\WINDOWS\SYSTEM32\WINRESUME.EXE?
(Command)
Display basic TCP/IP configuration, such as IP address, subnet mask, and default gateway.
(Command)
Display TCP/IP settings, including your Media Access Control (MAC) address, domain name system (DNS) server, and lease information.
(Command)
Release your IP address.
ipconfig /renew
What does this command do?
ping <IP address>
(Command)
Display TCP/IP protocol statistics and connection information. Can be used to see who is connected to your system; what ports are open; and if you use an -o switch, what the process ID is of the program that opened the port.
(Command)
Troubleshoot DNS problems. For example, you can get a listing of all the records in DNS using this.
(Command)
arp
(Command)
View a list of running processes.
(Command)
Terminates a process when you supply the process id.
Mirrored disk striping. RAID level x is also known as RAID 1+0 because it is disk striping while mirroring the data written in the stripe.
Disk striping with parity (RAID x volume). With RAID x volumes, the data is written to multiple drives along with parity information that is used to help recover data if a single drive fails. RAID x volumes need a minimum of three disks.
Disk mirroring/duplexing (mirrored volume). With disk mirroring, the data is written to both drives involved in the mirror to provide data redundancy. Windows 7 supports disk mirroring.
Disk striping (striped volume). With RAID level x, the data is split across drives with no data redundancy. RAID level x improves read and write performance by writing to multiple drives at the same time. You need a minimum of two drives.
(Win32 Command)
Check your hard drive for problems with the file system and for bad sectors.
(Win32 Command)
Make changes to Registry values; can be used to make selective backups. Prior to
(Win32 Command)
Used from the command line to defragment a hard drive.
(Win32 Command)
Back up files to tape or any writable file system.
This command verifies that system files have not been modified; or, if they have, replaces them with the original. It works with the hiddenC:\windows\system32\dllcache directory and the original operating system CD.
(Win32 Command)
See running programs and services, terminate problems, and view rudimentary performance information about the system.
(Win32 Command)
View detailed performance information
(Win32 Command)
Reconfigure the boot process for troubleshooting and diagnosing the boot process.
(Win32 Command)
View hardware and configuration information for your computer.
Logging component of the operating system; the central location for all logging activity.
What is C:\WINDOWS\SYSTEM32\WINLOGON.EXE?
(Types of Malicious Software)
Code that runs on a computer without the user’s knowledge; it infects the computer
when the code is accessed and executed.
(Types of Malicious Software)
Much like viruses except that they self-replicate whereas a virus does not.
(Types of Malicious Software)
Appear to perform desired functions but are actually performing malicious
functions behind the scenes.
(Types of Malicious Software)
Type of malicious software that is either downloaded unwittingly from a website
or is installed along with some other third-party software.
(Types of Malicious Software)
Software designed to gain administrator-level access to the core of a system
without being detected.
The act of manipulating users into revealing confidential information or
performing other actions detrimental to the user.
The verification of a person’s identity, it helps protect against unauthorized
access.
The four types of Authentication.
A security feature in Windows 7/Vista which requires administrative login to perform
higher tasks.
The act of changing information using an algorithm known as a cipher to make it
unreadable to anyone except users who possess the proper “key” to the data.
A feature of Windows which encrypts one or more files or folders directly within the
Properties page. Makes files appear green.
A feature of Windows which encrypts an entire disk, available only on Windows 7 Ultimate/Enterprise and
Vista Ultimate/Enterprise. Requires TPM.
The 3 methods of Hard Drive Disposal.
In regard to permissions- If you create a folder, the default action it takes is:
In regard to permissions- If you move a folder within the same partition, it:
In regard to permissions- If you move or copy a folder to another partition, the (new) folder:
This command is used to repair Bootmgr
This command rewrites the master boot
record in Vista/7/8.
This command rebuilds the boot configuration data store.
This command repairs the Master Boot Record in Windows XP.
This command writes new boot sector information in Windows XP.
6 steps of the laser printing process.
This type of printer uses force to transfer ink to paper, for example, a print head striking a ribbon with
paper directly behind it, similar to a typewriter.
Also known as an electrophotographic printer
This type of printer produces text and images by heating specially coated paper.
This type of printer works by propelling ink onto various sizes of paper.
The four most common motherboard form factors.
This file contains setup errors during an installation of Windows.
Maximum number of partitions on one hard drive.
What is different about an active partition?
Any section of a hard drive with a letter is called
a ____________.
Malware is short for:
Port 80
Port 443
Port 25
Port 23
Port 110
Port 445
Port 995
In this type of attack, a vast number of
compromised computers are to flood
a specific server at the same time for the purpose of making that server and its services
unavailable.
In this type of attack, one computer and one internet connection is used to flood a server with packets, with the aim of overloading the targeted server’s bandwidth and resources.
Provide an example of a T-Carrier service.
True/False:
An Ethernet cable can be considered a display cable.
What is ADSL?
What is SDSL?
DVI-A
DVI-D
DVI-I
What type of DVI connector is shown?
What type of DVI connector is shown?
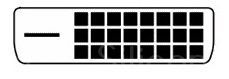
What type of DVI connector is shown?

What type of DVI connector is shown?

What type of DVI connector is shown?

Port 21
Port 53
Port 143
Port 3389
What is the color of a wire that reads +5 volts?
What is the color of a wire that reads -5 volts?
What is the color of a wire that reads +12 volts?
What is the color of a wire that reads -12 volts?
What is the color of a wire that reads +3.3 volts?
Intel or AMD?
Socket LGA
Intel or AMD?
Socket 775
Intel or AMD?
Socket 1155
Intel or AMD?
Socket 1156
Intel or AMD?
Socket 1366
Intel or AMD?
Socket 940
Intel or AMD?
Socket AM2+
Intel or AMD?
Socket AM3
Intel or AMD?
Socket AM3+
Intel or AMD?
Socket FM1
Intel or AMD?
Socket F
The device with SCSI ID _______ is always given the highest priority, as this ID is
normally set aside for the host adapter.
(Types of Social Engineering)
The act of trying to get people to give their user names, passwords, etc. by masquerading as someone else electronically.
(Types of Social Engineering)
Observing someone’s screen or keyboard to get information, often passwords.
(Types of Social Engineering)
When an unauthorized person tags along with an authorized person to gain entry to a
restricted area.
What is a TPM?
What does the "nb" in "nbtstat" stand for?
Which command line tool may be able to assist you in securing the open ports on a local workstation?
What does robocopy stand for?
The address below is an example of what?
169.254.31.29
What are the minimum system requirements for Windows XP?
What are the minimum system requirements for Windows Vista?
What are the minimum system requirements for Windows 7?
How many pins does a PC100 memory module have?
How many pins does a DDR-200 PC-1600 memory module have?
How many pins does a DD2-800 PC2-6400 memory module have?
How many pins does a PC3-12800 memory module have?
How many pins does a PC4-25600 memory module have?
How many pins does a PC800 RIMM have?
True or False?
SO-DIMMs of DDR and DDR2 both have 200 pins.
How many pins does a DDR3 SO-DIMM have?
How many pins does a UNIDIMM memory module have?
(Win32 Command)
Diagnostic tool for getting information about and testing a
computer’s DirectX version.
(Win32 Command)
MSTSC
Identify the laptop adapter card shown:
Identify the laptop adapter card shown:
Identify the laptop adapter card shown:
What is the maximum range of a Class 1 Bluetooth device?
What is the maximum range of a Class 2 Bluetooth device?
What is the maximum range of a Class 3 Bluetooth device?
VDSL
Identify the connector shown:

Identify the connector shown:

Identify the connector shown:

Identify the connector shown:

Identify the connector shown:

What type of Cat5 cable is shown?

What type of Cat5 cable is shown?

What are the 3 private IP address ranges?
What is a RAM "channel", and how does it affect speed?
What is a BD-R disc?
What is a BD-RE disc?
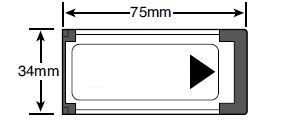
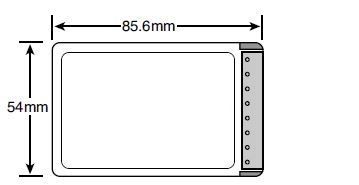
Identify the type of memory card shown:
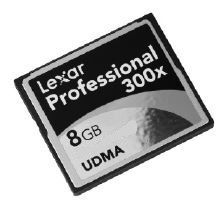
Identify the type of memory card shown:

Identify the type of memory card shown:

Identify the type of memory card shown:

Identify the type of memory card shown:

Identify the type of memory card shown:

Name the connector shown:
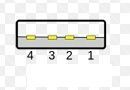
Name the connector shown:

Name the connector shown:

Name the connector shown:

Name the connector shown:

Name the connector shown:

USB 1.1
USB 2.0
USB 3.0
Firewire AKA Firewire 400
Firewire 800
SATA Rev. 1
SATA Rev. 2
SATA Rev. 3
eSATA
802.11a
802.11b
802.11g
802.11n
Who wins?
Explicit or Inherited permissions?
What is the difference between a RAM chip that is Single-Sided vs Double-Sided?
______ humidity and _______ temperature can contribute to ESD.
What is the Resolution of VGA?
What is the Resolution of SVGA?
What is the Resolution of XGA?
Who wins?
Allow or Deny permissions?
What is the Resolution of WXGA?
What is the Resolution of SXGA?
Refresh Rate vs Response Time:

 Hide known cards
Hide known cards